Inside Microsoft 365 Defender: Solving cross-domain security incidents through the power of correlation analytics - Microsoft Security Blog
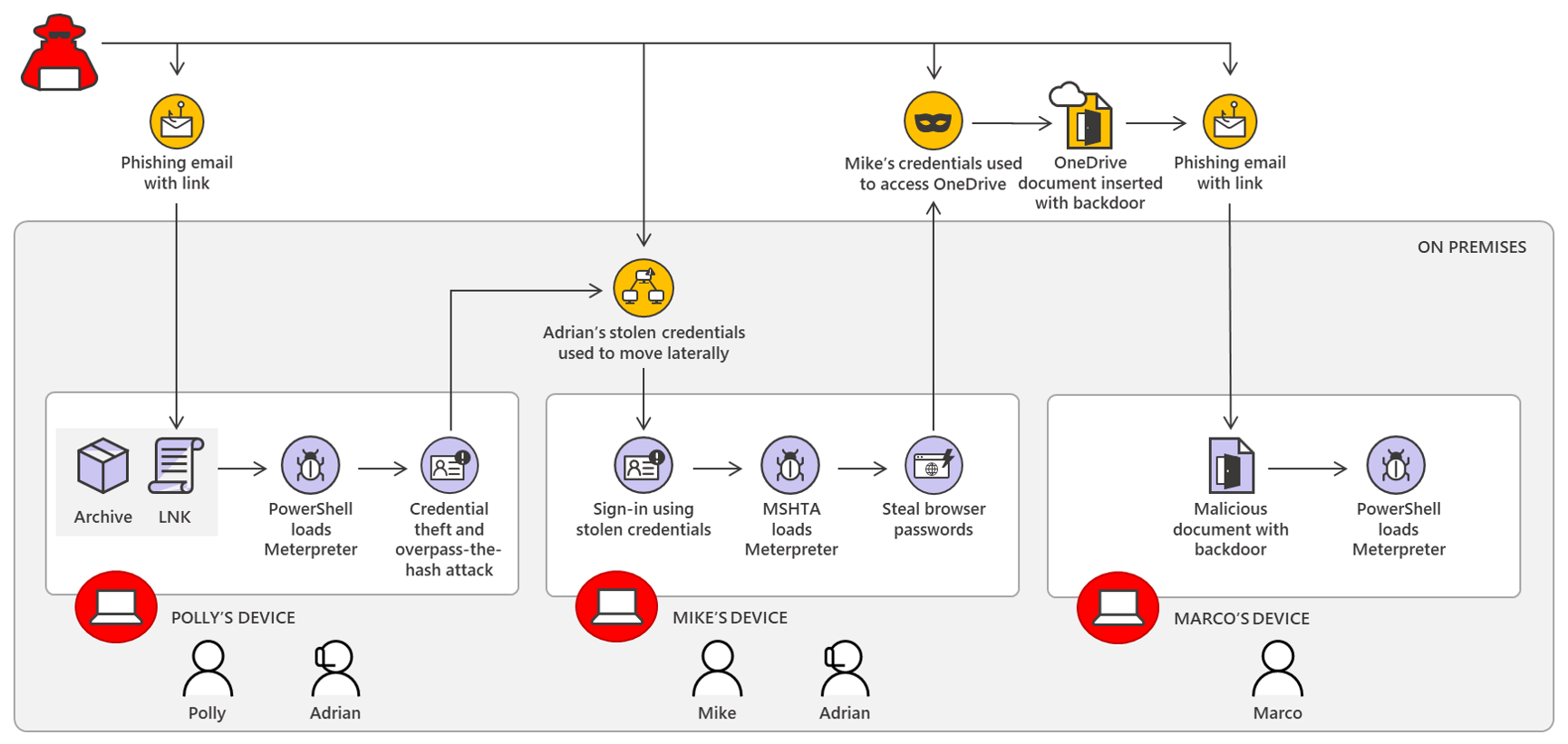
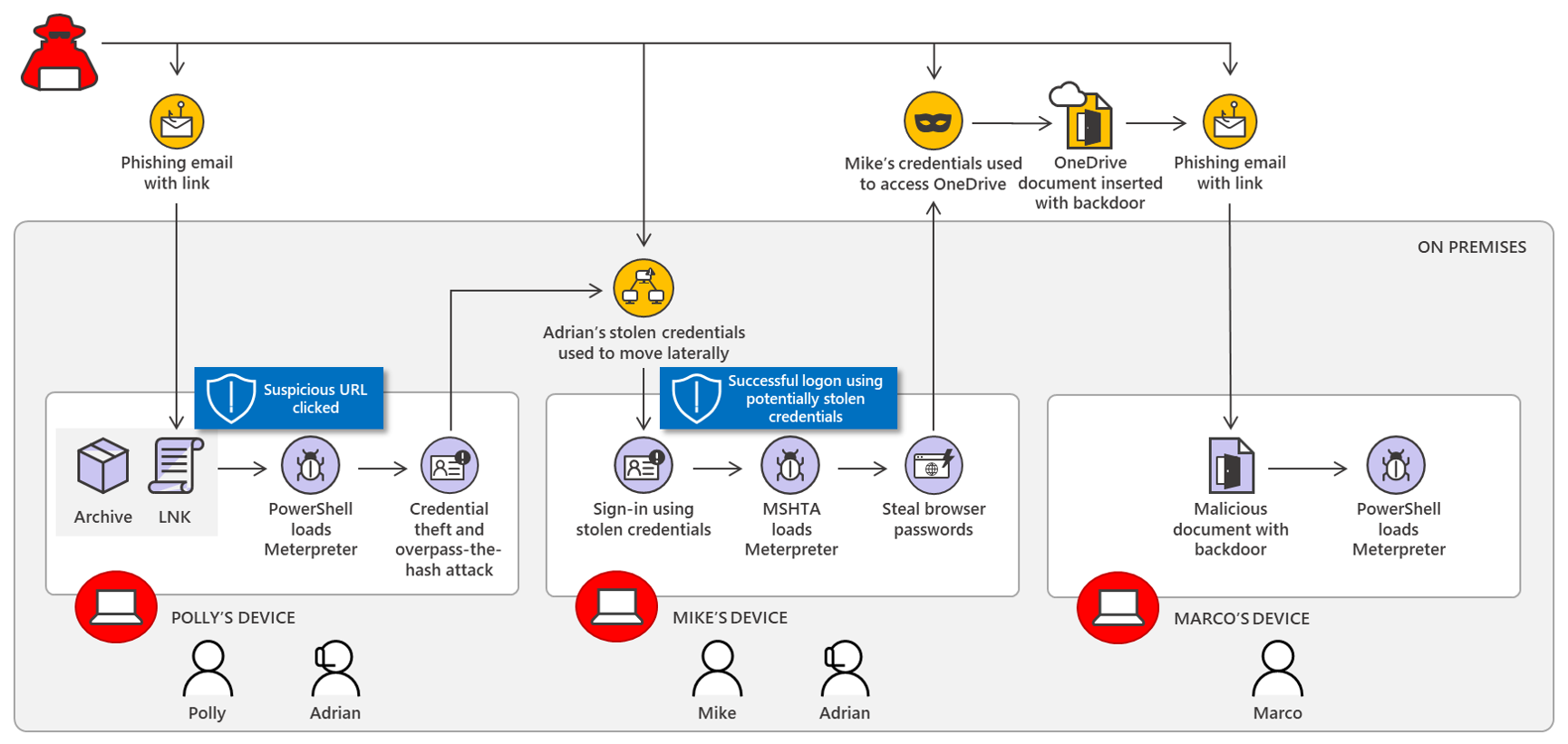
Inside Microsoft 365 Defender: Solving cross-domain security incidents through the power of correlation analytics - Microsoft Security Blog
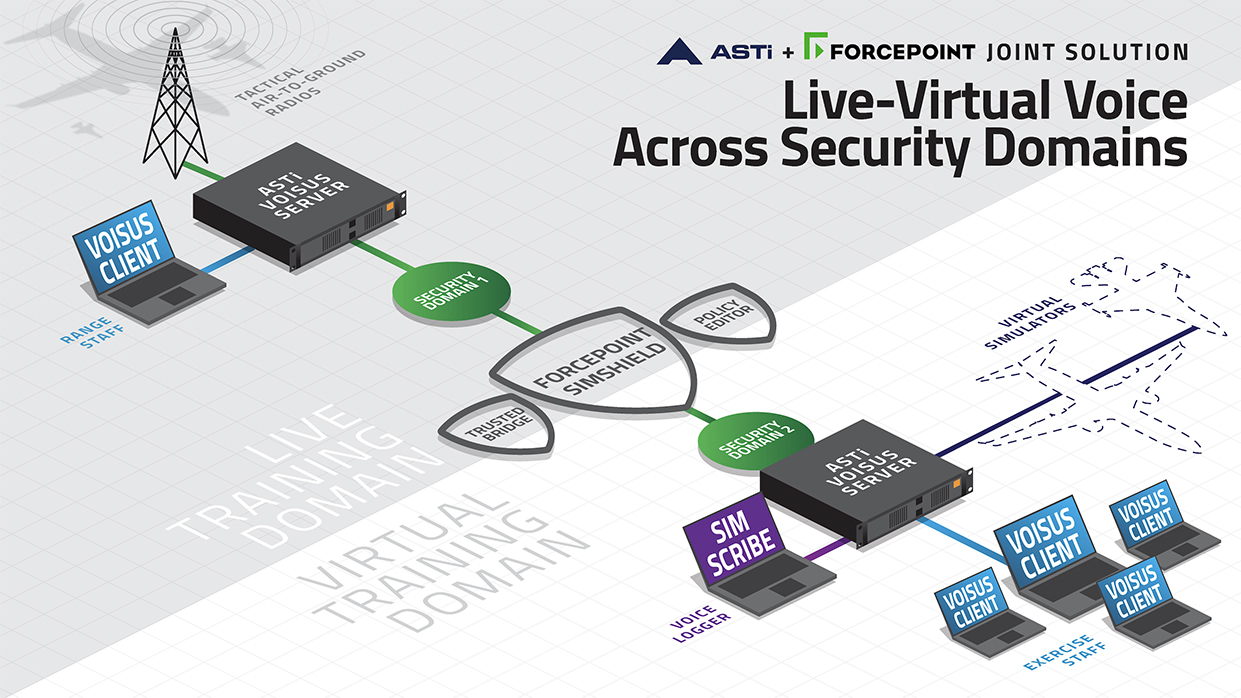
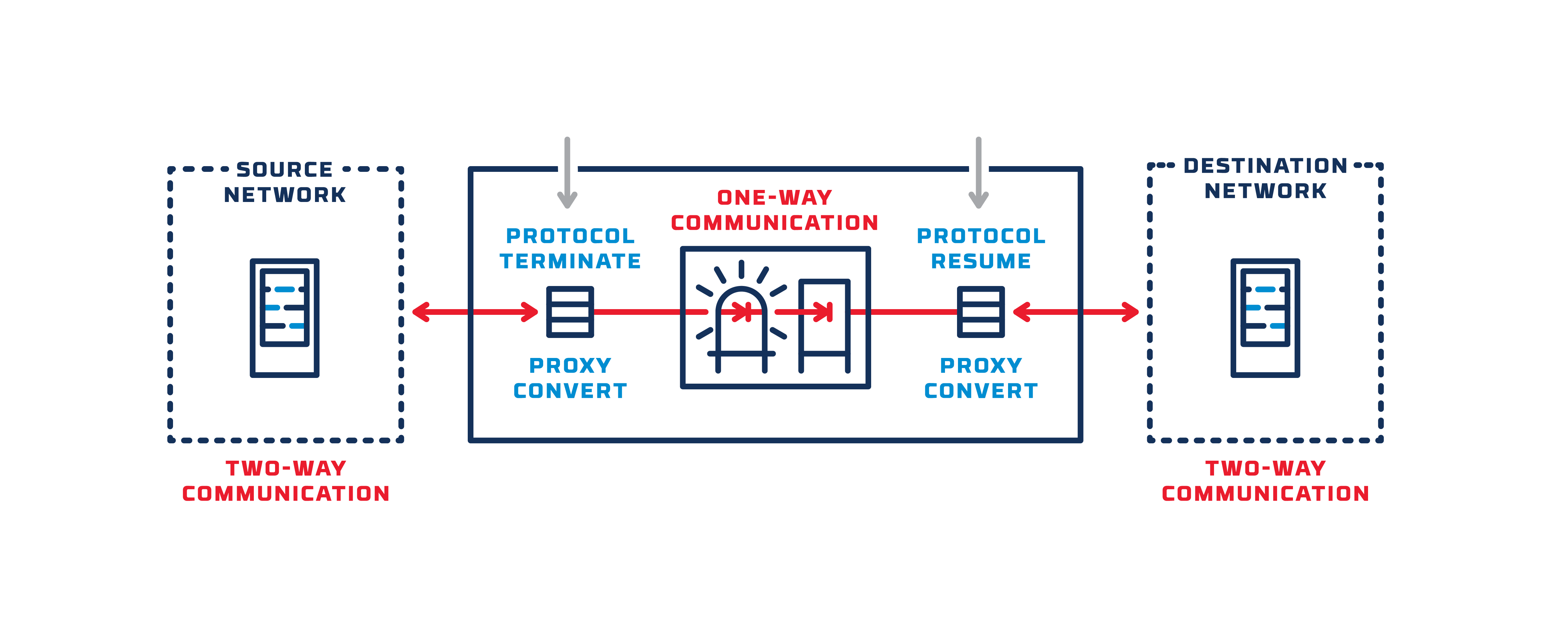
ASTi and Forcepoint form Alliance to Provide Cross-Domain Solution for Live-Virtual Voice Communications

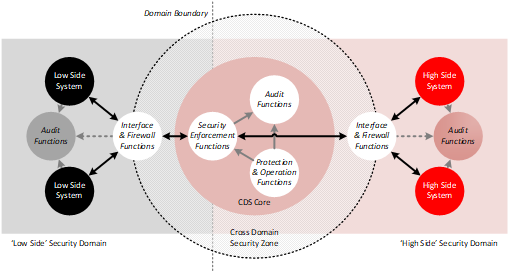
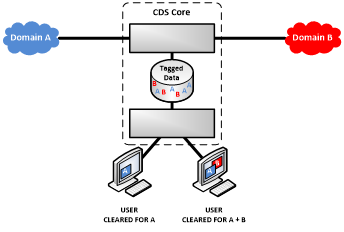





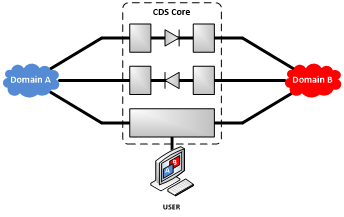
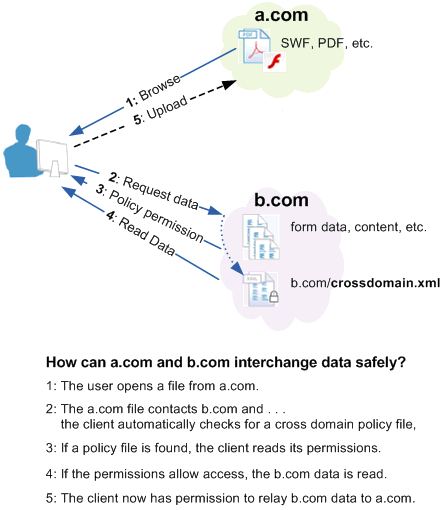
![PDF] A cloud-oriented cross-domain security architecture | Semantic Scholar PDF] A cloud-oriented cross-domain security architecture | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/0504aa0445aed2c95adcc84ce0bb474c6dc9ed44/4-Figure1-1.png)