Figure 2 from Man-In-The-Middle attacks on bluetooth: a comparative analysis, a novel attack, and countermeasures | Semantic Scholar
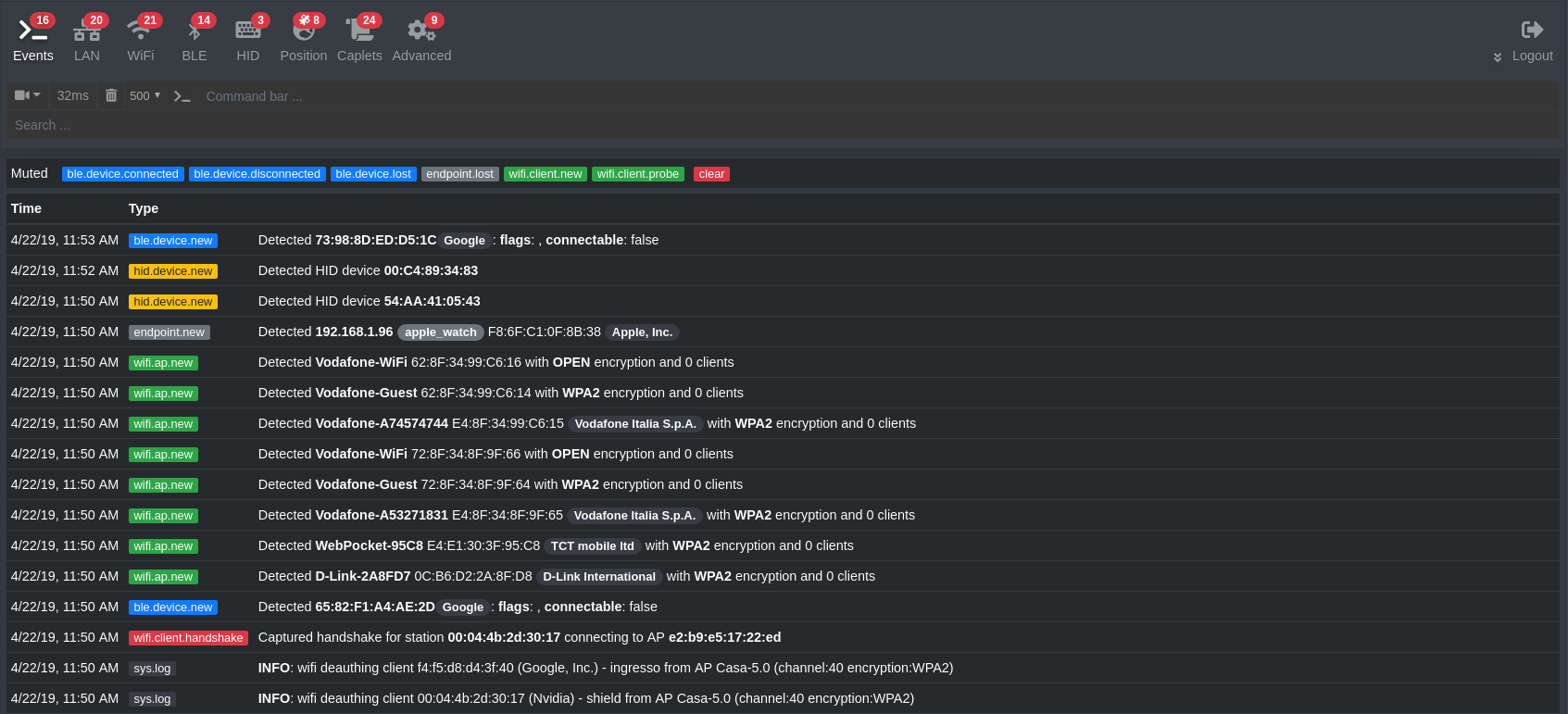
Bluetooth-Sniffing Highway Traffic Monitors Vulnerable to MITM Attack | The Security Ledger with Paul F. Roberts
GitHub - PaulPauls/Bluetooth_LE_MITM: Man-in-the-Middle Relay program between a Bluetooth Low-Energy (BTLE) Peripheral and Central
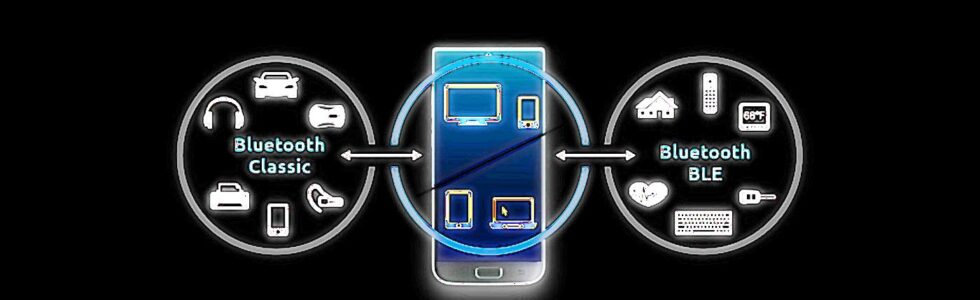
National CSIRT-CY | National Computer Security Incident Response Team of Cyprus - BLURtooth vulnerability lets attackers defeat Bluetooth encryption
![PDF] A Novel Bluetooth Man-In-The-Middle Attack Based On SSP using OOB Association model | Semantic Scholar PDF] A Novel Bluetooth Man-In-The-Middle Attack Based On SSP using OOB Association model | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/58bf1873844a200e705c37e28a746ae3343a8eeb/3-Figure2-1.png)











![How to Prevent Man in the Middle Attacks [with Examples] - Security Boulevard How to Prevent Man in the Middle Attacks [with Examples] - Security Boulevard](https://www.firstpoint-mg.com/wp-content/uploads/2020/01/IMSI-featured-300x235.png)